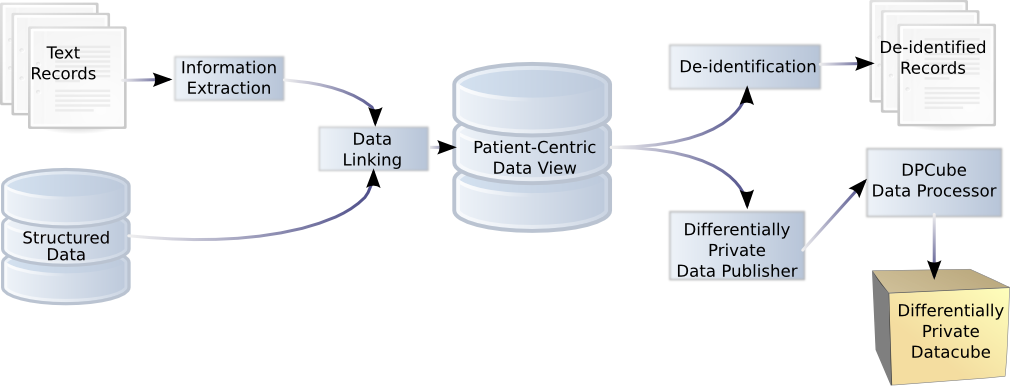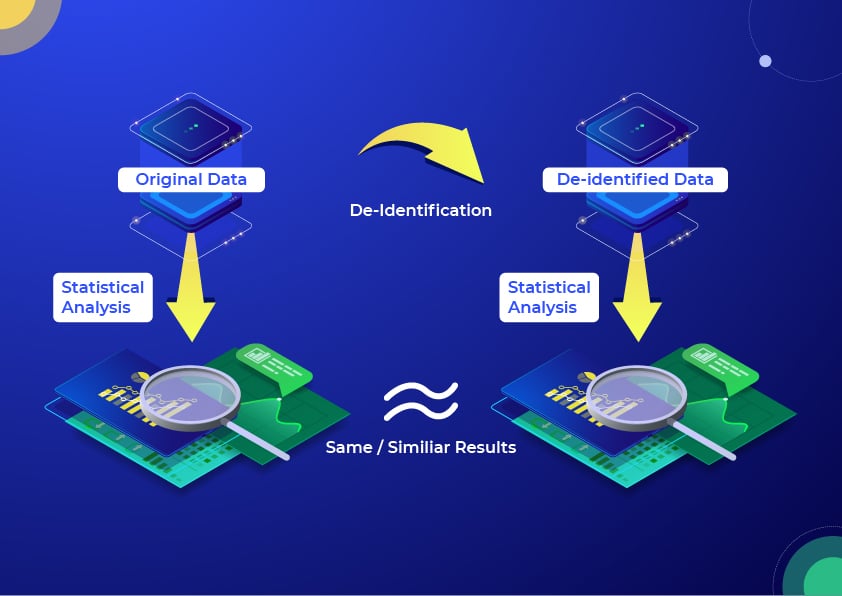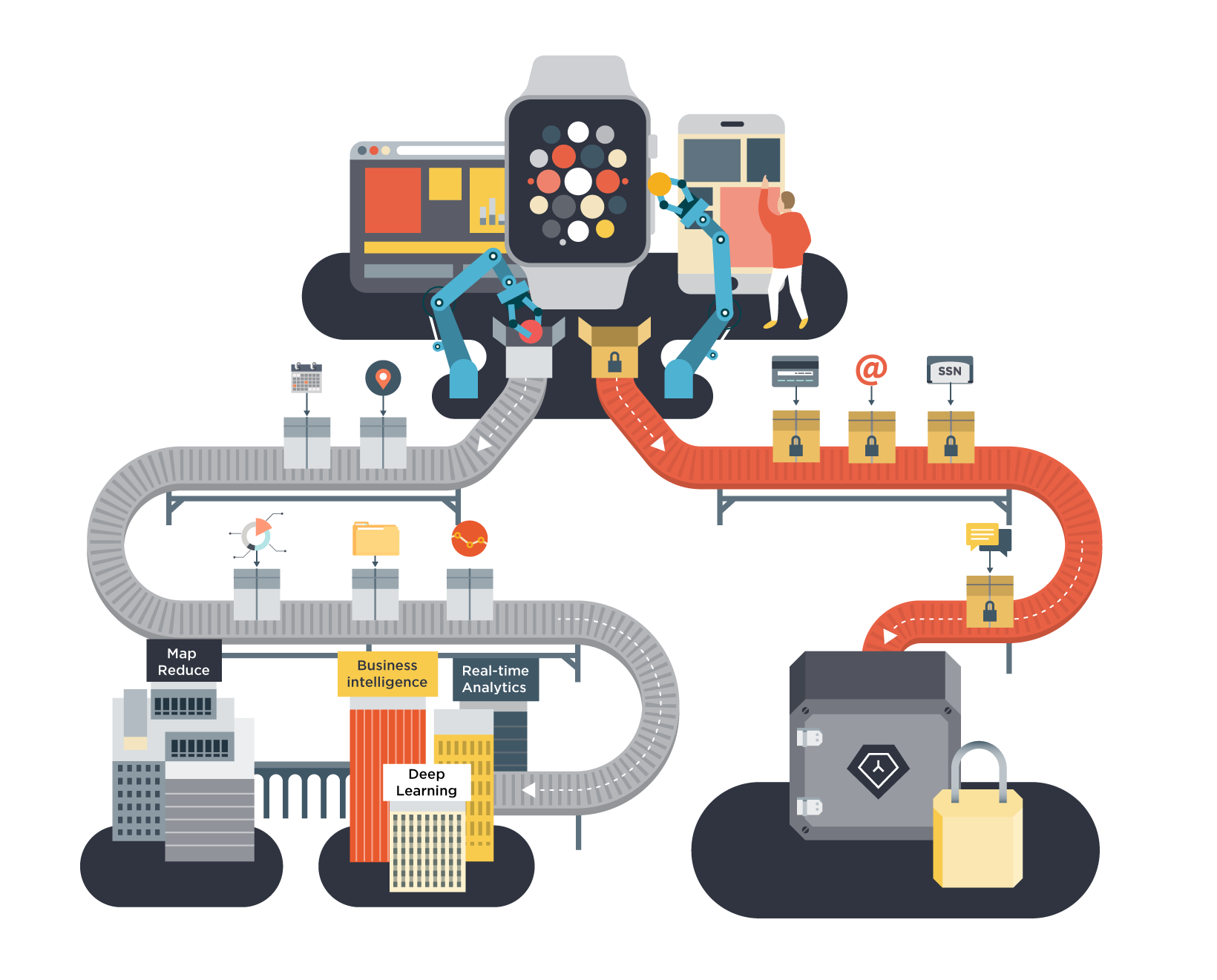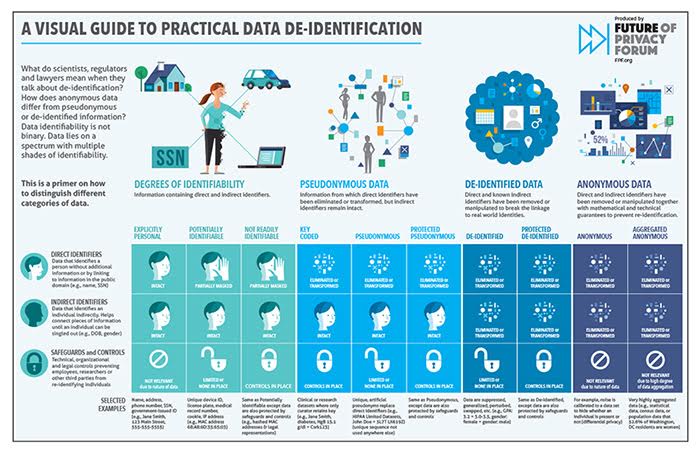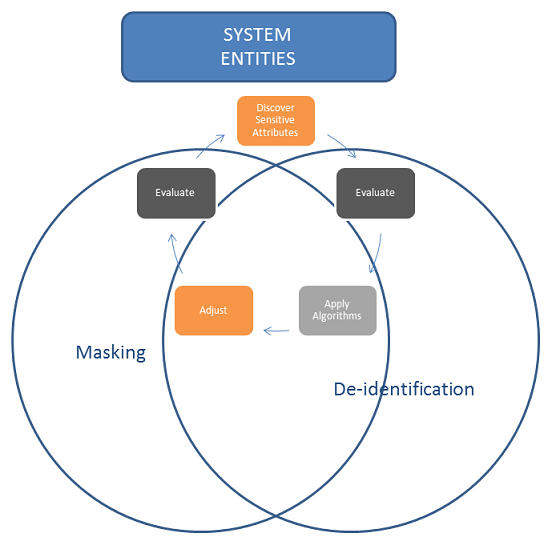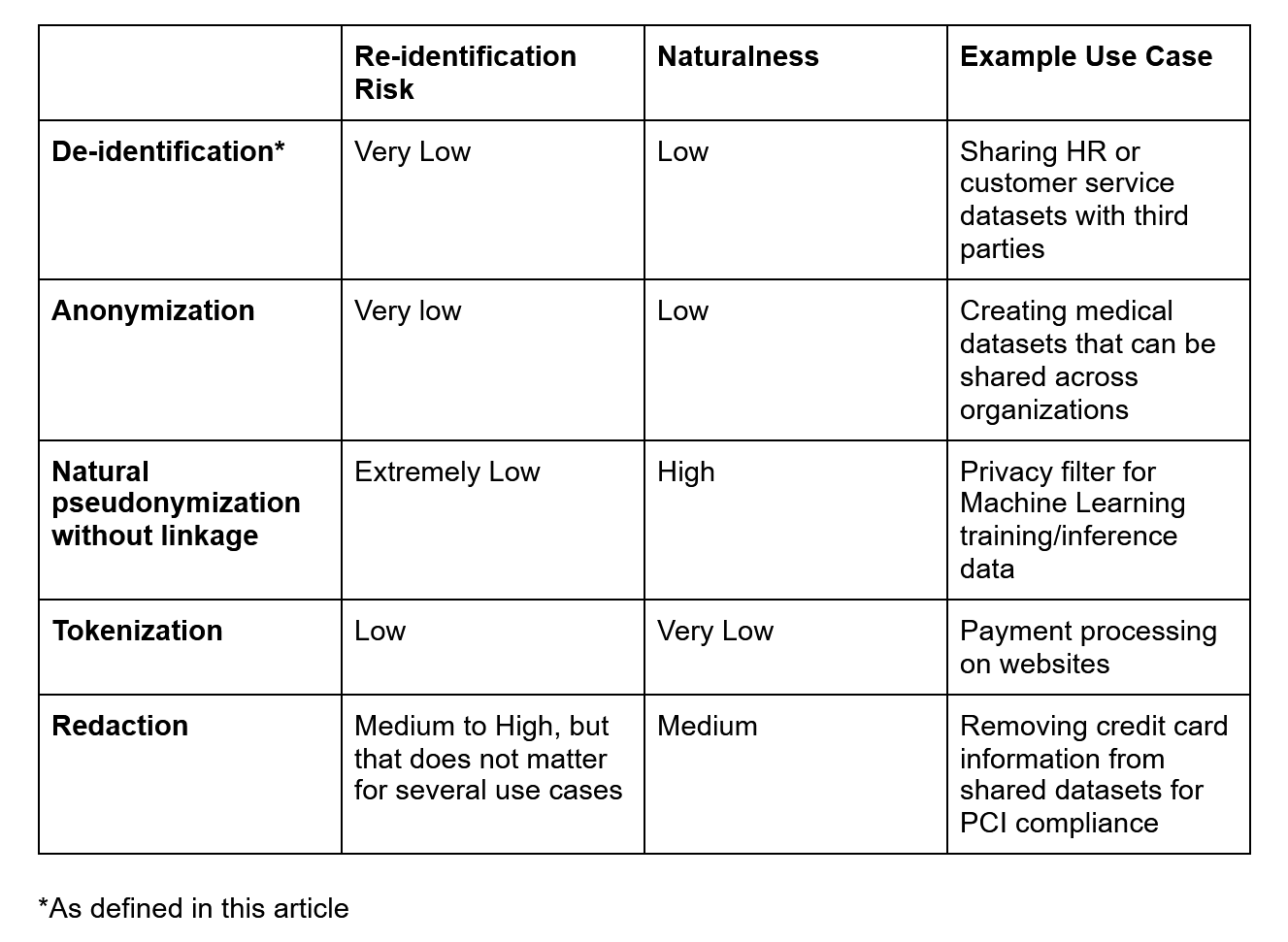
Demystifying De-identification. Understanding key tech for data… | by Patricia Thaine | Towards Data Science

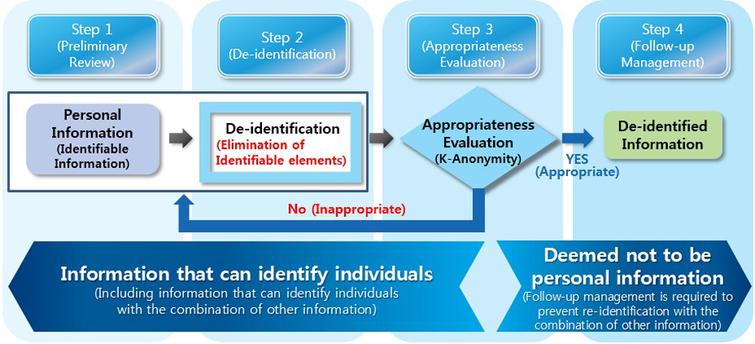
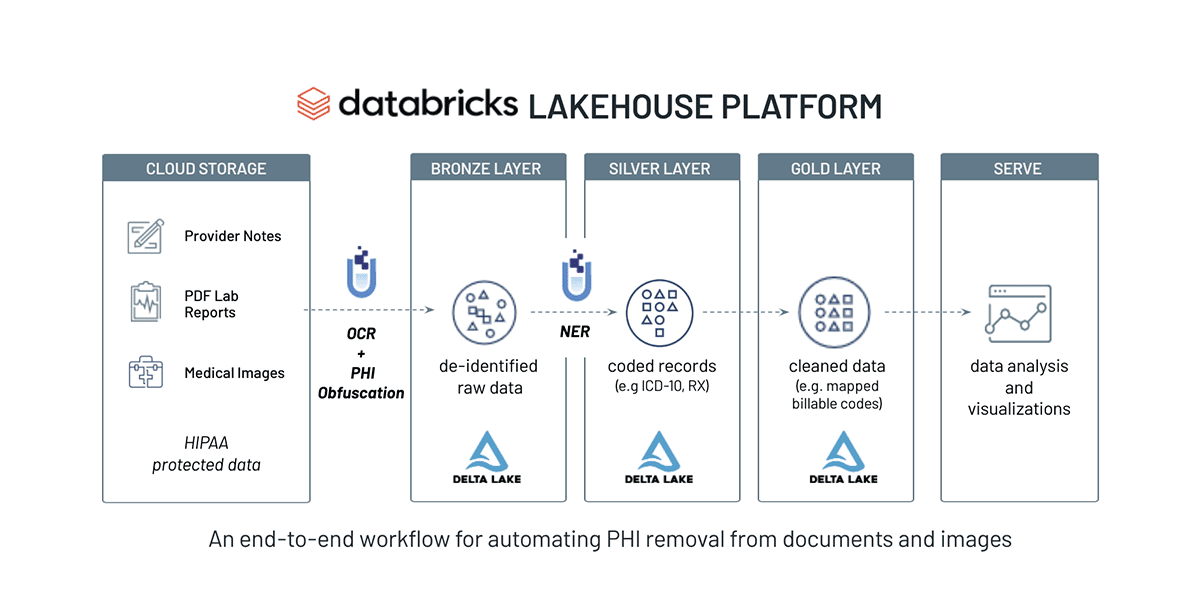
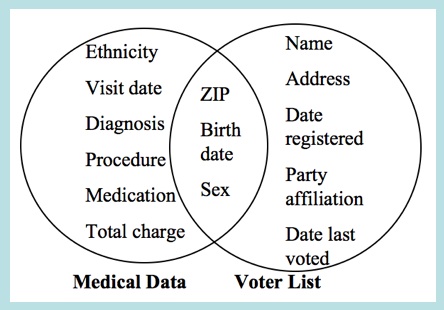
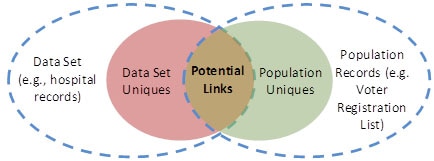
HIPAA De-identification example. Protected Health Identifiers were... | Download Scientific Diagram
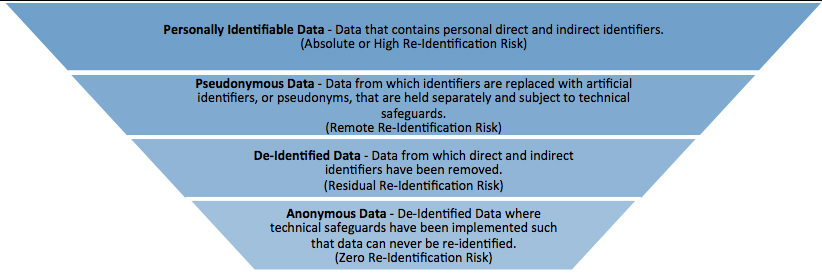
Bryan Cave Leighton Paisner - At A Glance: De-Identification, Anonymization, and Pseudonymization under the GDPR