What Is Data Center Security? 6 Ways to Ensure Your Interests Are Protected - Hashed Out by The SSL Store™

Are Encrypted Lockboxes for Data Centers Worth the Usability Cost? | Data Center Knowledge | News and analysis for the data center industry
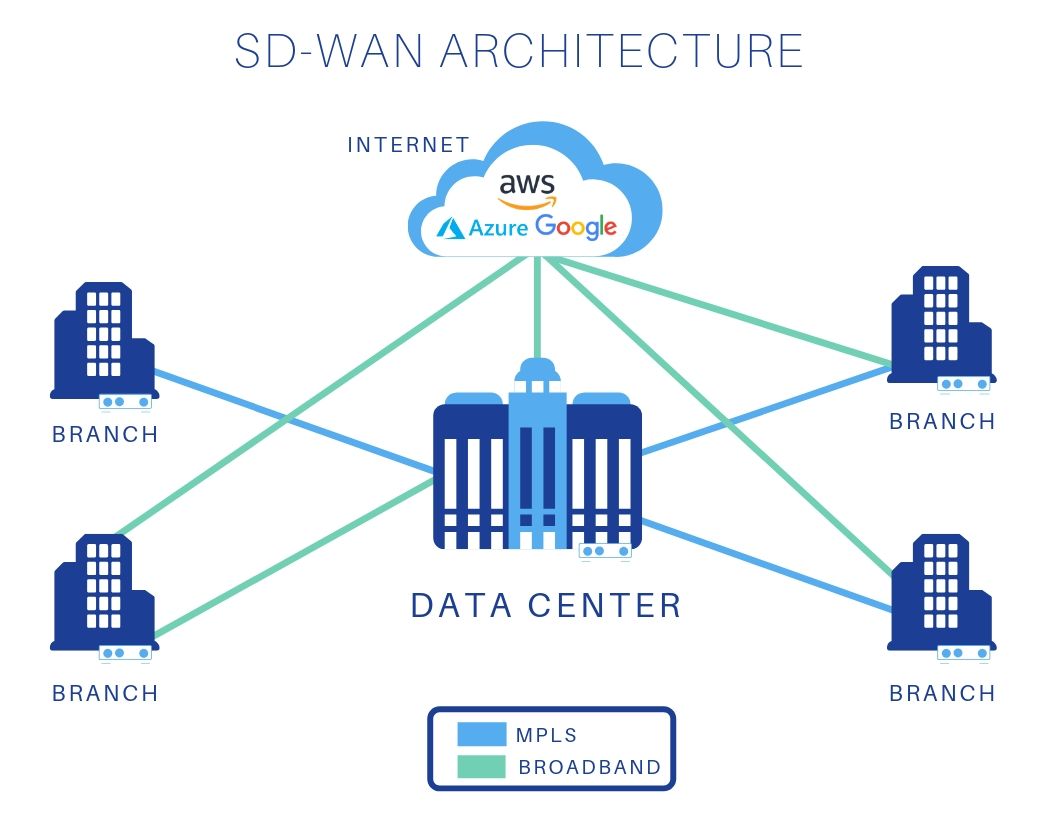
The Critical Role Data Centers Play in Today's Enterprise Networks: Part 2 – How SD-WAN is Streamlining the Enterprise and Attendant Data Centers

Symmetry | Free Full-Text | Efficient Hierarchical Identity-Based Encryption System for Internet of Things Infrastructure

Isometric Data Flow Processing Data Protection Encryption Process Server Room Stock Vector Image by ©modpic #196866632
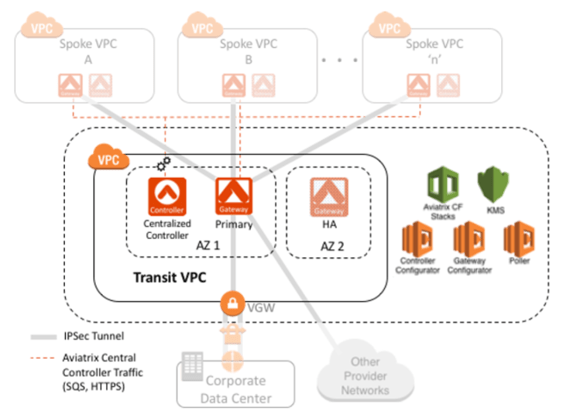
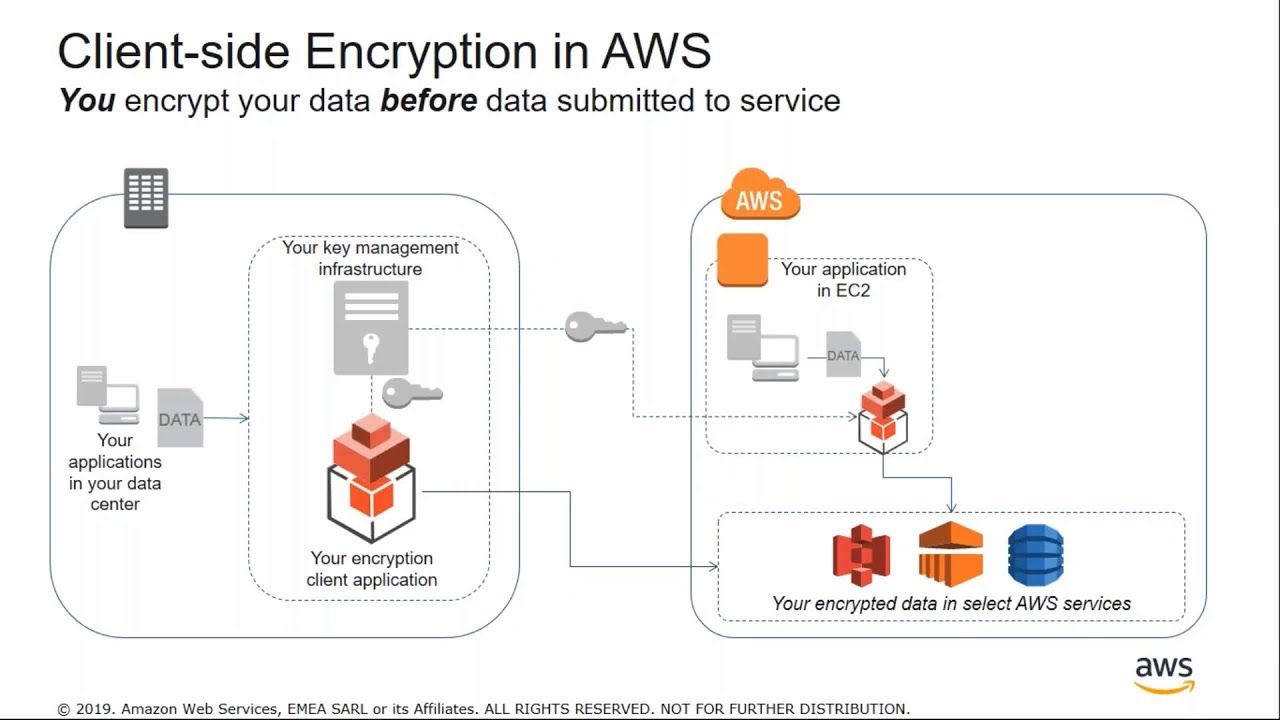
How should I encrypt data-in-motion between my data center and the AWS Global Transit VPC? - Aviatrix

Center for Data Innovation - What Will Be the Impact of the UK's Online Safety Bill on Encryption and Anonymity Online? - Center for Democracy and Technology

Google Boosting Encryption Between Data Centers | Data Center Knowledge | News and analysis for the data center industry

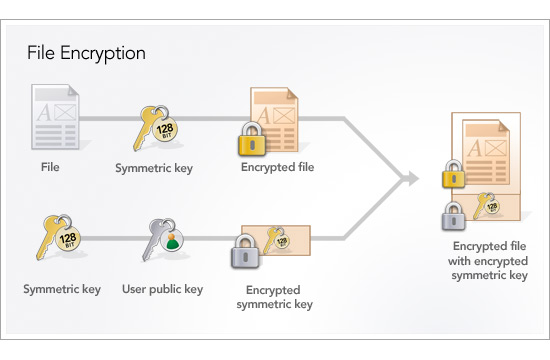
Data encryption involving authentication, authorizations, and identity management | Titan Power Blog