Olaudah Equiano® on Twitter: "The letter Senator Ike Ekweremadu wrote to the British High Commission Abuja, to support the visa application of the minor, Ukpo Nwamini David, who was supposed to donate

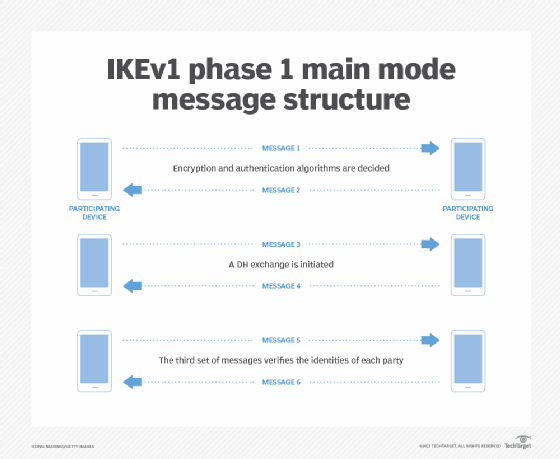
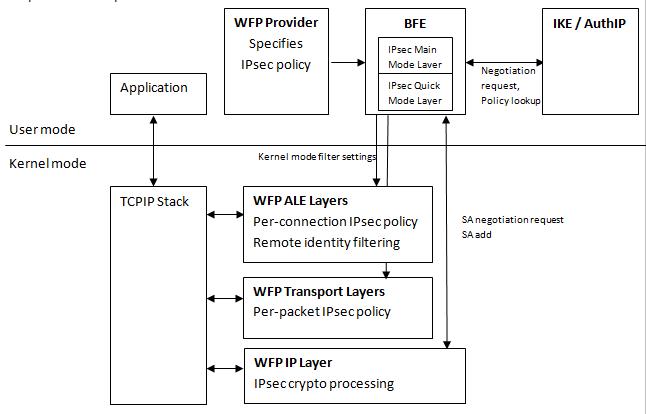
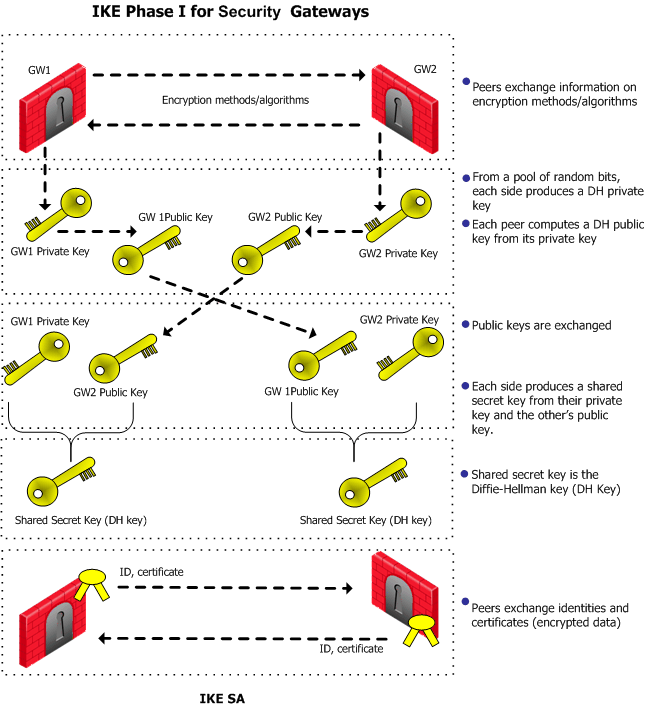
Using an ACL to Establish an IPSec Tunnel - AR500, AR510, and AR530 V200R007 CLI-based Configuration Guide - VPN - Huawei