Securing color image transmission using compression-encryption model with dynamic key generator and efficient symmetric key distribution | Semantic Scholar
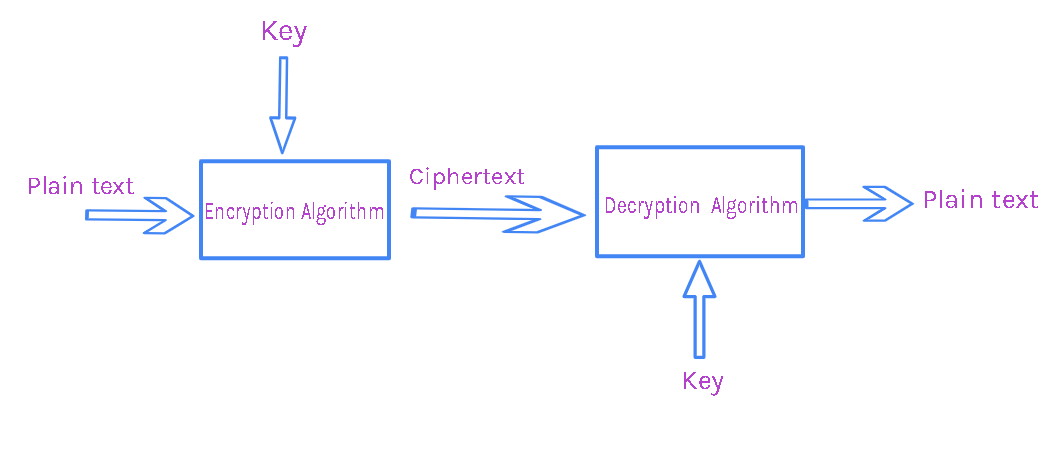
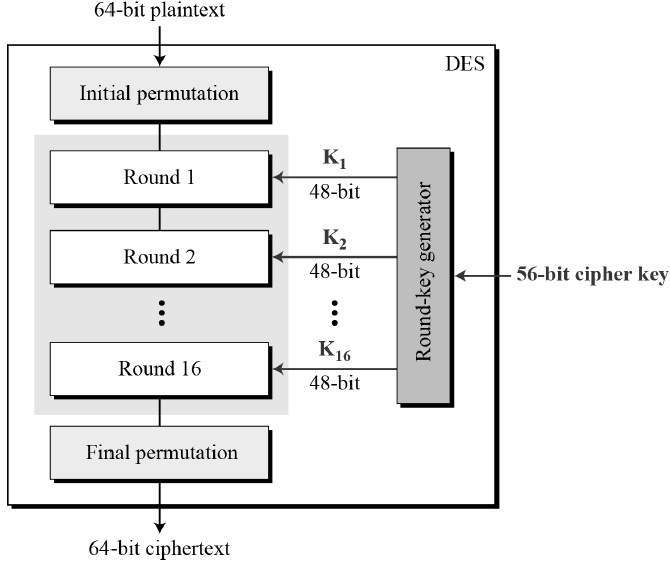
![PDF] ANALYSIS AND COMPARISON OF SYMMETRIC KEY CRYPTOGRAPHIC ALGORITHMS BASED ON VARIOUS FILE FEATURES | Semantic Scholar PDF] ANALYSIS AND COMPARISON OF SYMMETRIC KEY CRYPTOGRAPHIC ALGORITHMS BASED ON VARIOUS FILE FEATURES | Semantic Scholar](https://d3i71xaburhd42.cloudfront.net/d592d1cea5d1e125996903090d8d18773ede235f/4-Figure1-1.png)
PDF] ANALYSIS AND COMPARISON OF SYMMETRIC KEY CRYPTOGRAPHIC ALGORITHMS BASED ON VARIOUS FILE FEATURES | Semantic Scholar

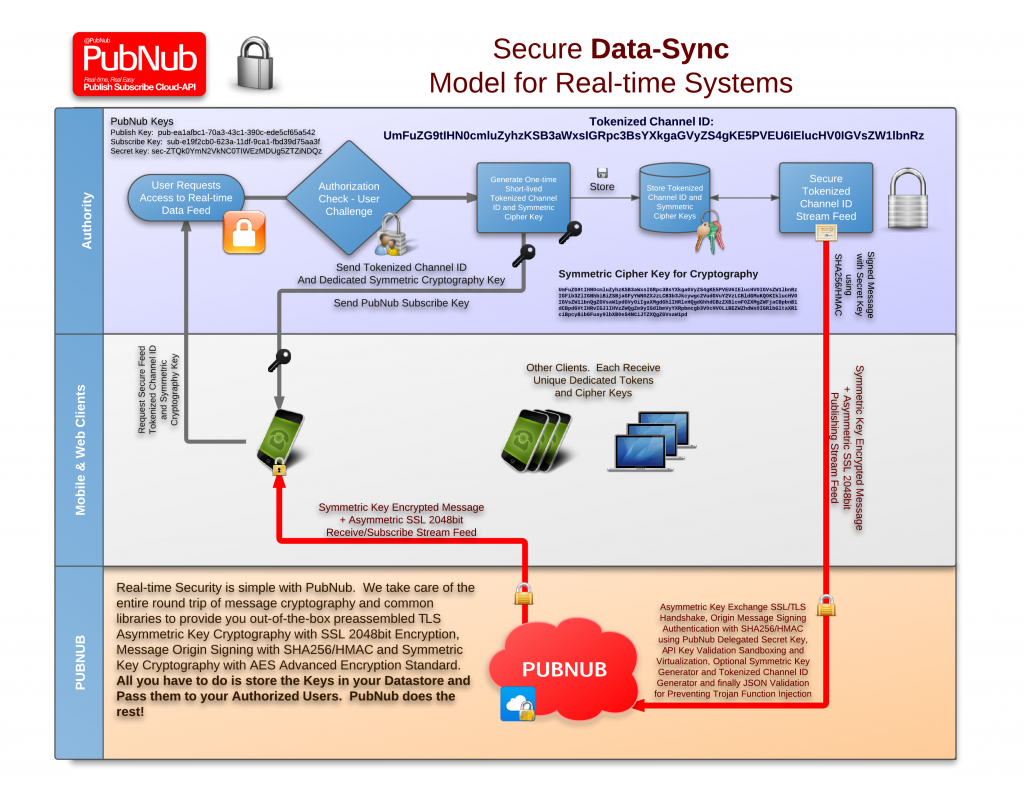
Securing color image transmission using compression-encryption model with dynamic key generator and efficient symmetric key distribution - ScienceDirect
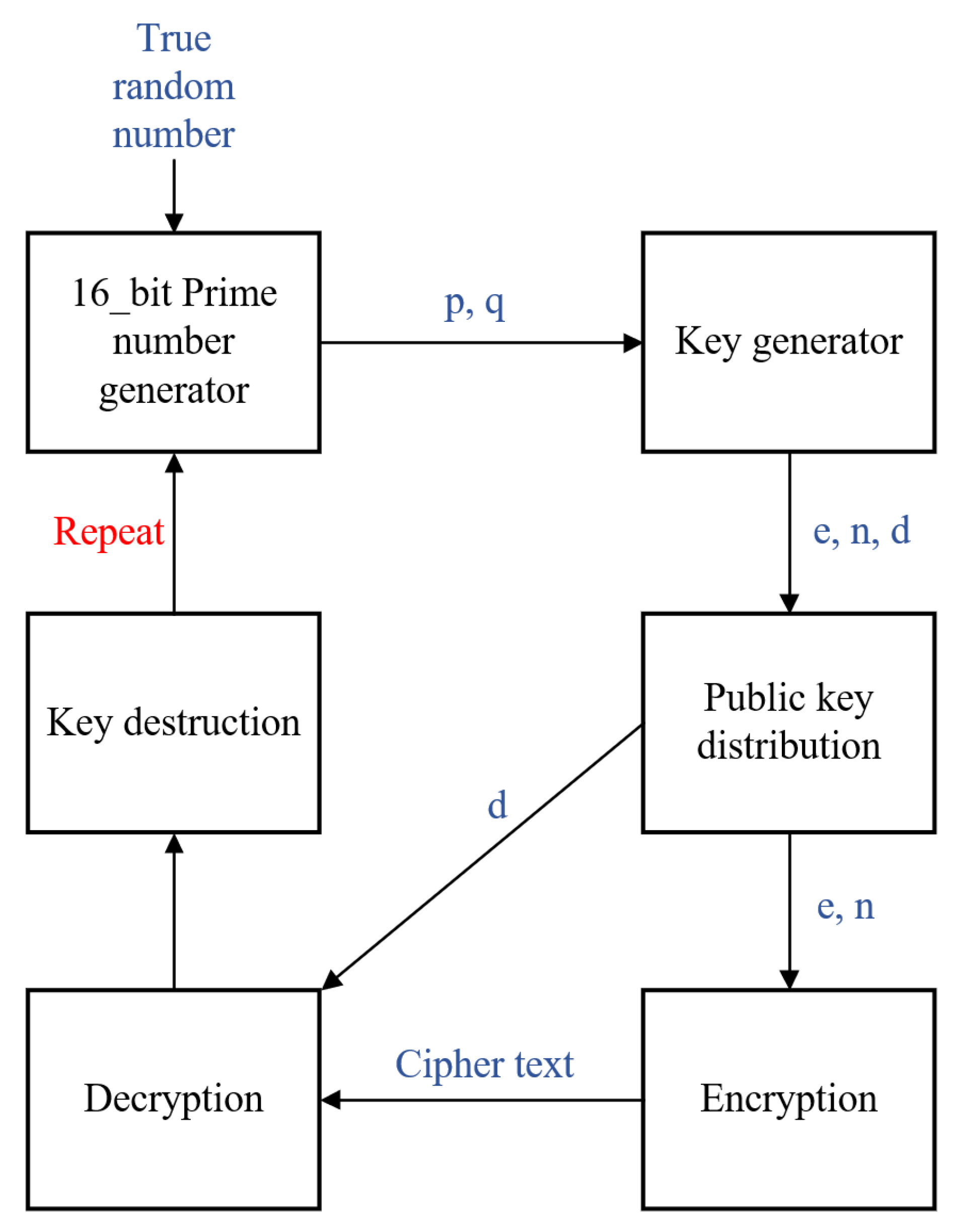
Electronics | Free Full-Text | New RSA Encryption Mechanism Using One-Time Encryption Keys and Unpredictable Bio-Signal for Wireless Communication Devices
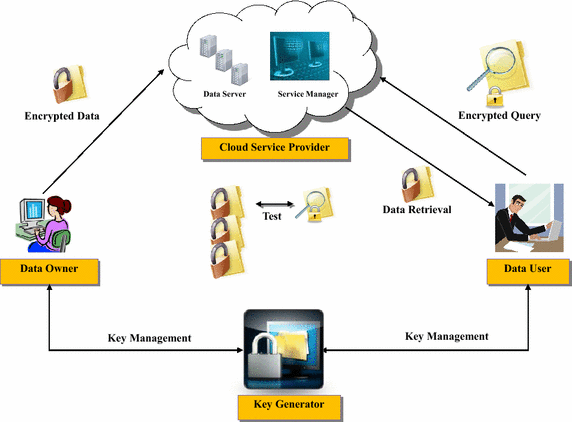
Implementation of searchable symmetric encryption for privacy-preserving keyword search on cloud storage | Human-centric Computing and Information Sciences | Full Text




![What Is AES Encryption? [The Definitive Q&A Guide] What Is AES Encryption? [The Definitive Q&A Guide]](https://www.trentonsystems.com/hs-fs/hubfs/symmetric%20crytography%20opt.jpg?width=1002&name=symmetric%20crytography%20opt.jpg)